
A powerful POS system that hustles as hard as you do
That’s a given. But our all‑in‑one are so much more. and easily with powerful that help tackle everything from to programs and everything in between.
Rates starting at 2.3% + 10¢
A full POS in the palm of your hand
Our handheld POS with built‑in printer and barcode scanner lets you take orders tableside and process payments on the go.
Learn about FlexFast, flexible funding for your business
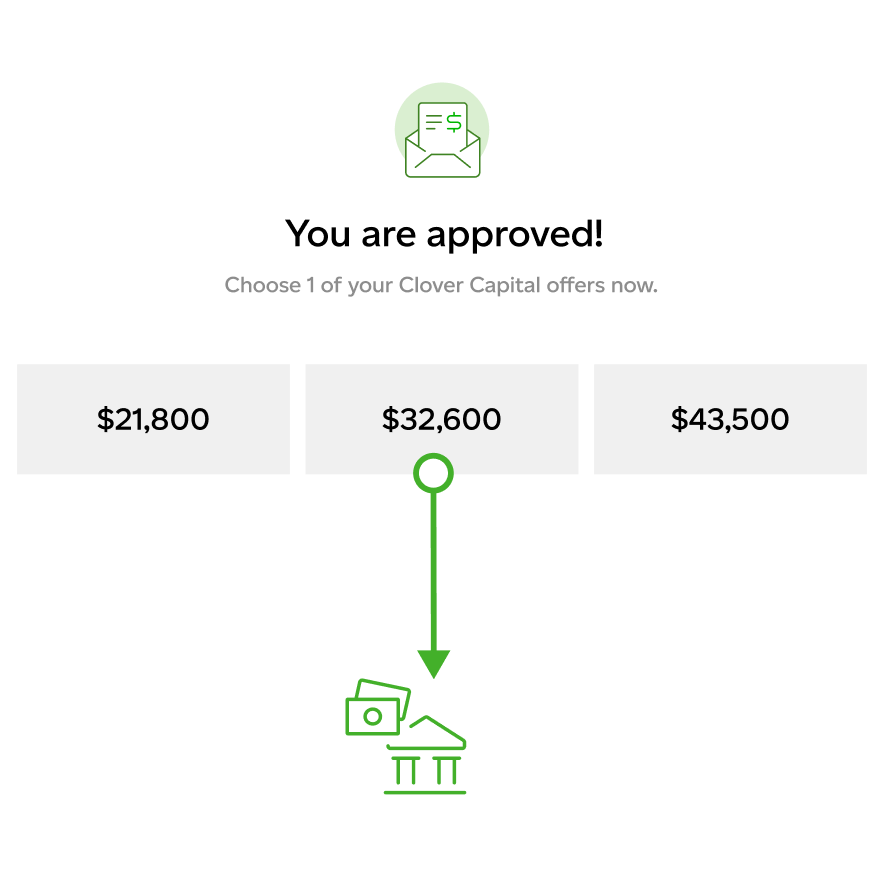
Clover Capital
Learn more
Learn moreGet the flexibility to grow your business by turning future sales into working capital with Clover Capital.
- With approvals typically granted in 1-2 business days, you’ll see working capital in your account just 2-3 days after you’re approved.
- Payments are a fixed percentage of sales—not a fixed amount—so you pay more when your sales are strong and less if sales slow down.
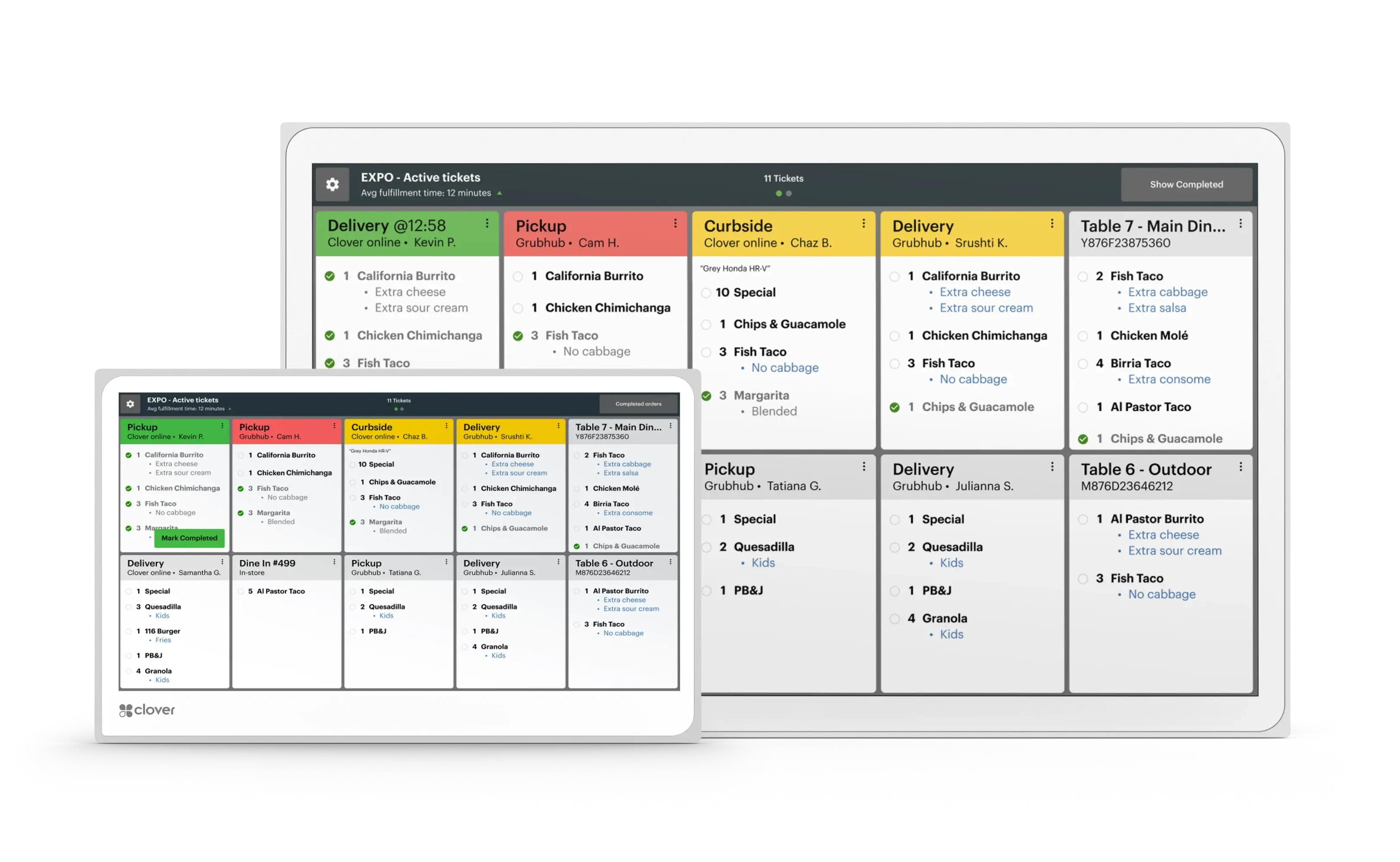
One system. Built for every kind of business.

From quick counter transactions to full tableside service, Clover lets you accept payments anywhere.
Map tables, manage your menu, customize orders, and more with software that lets service shine.
With countertop stations, handheld devices, and a KDS, we’ve got hardware for restaurants of all sizes.
Manage online orders, reservations, loyalty programs, and more with an ample selection of apps.
Accept credit, debit, gift cards, and contactless payments, plus fast refunds, returns, and exchanges.
Easily itemize receipts, track product versions, run reports, and manage your employees.
Regardless of the retail business you’re in, we’ve got what you need to keep it all running.
Manage multiple locations, add an online shop, sync sales data, and more with pre‑built app integrations.
Send invoices, set up recurring payments, and keep payment info on file for your regulars.
Manage business from your virtual dashboard whether at the office, in the field, or on the road.
Mobile payments and the Go app give you the freedom to accept payments virtually anywhere.
Manage bookings, get customer insights, sync with your payroll software, and more.
Small businesses use Clover to get the job done










 With approvals typically granted in 1-2 business days, you’ll see working capital in your account just 2-3 days after you’re approved.
With approvals typically granted in 1-2 business days, you’ll see working capital in your account just 2-3 days after you’re approved.
